You can evaluate events based on the Computer, Event Log, Event Source, Event ID's, Event Categories, and etc. In the event that the event message found match your specified criteria, the alerts tied to this entry can be triggered.
From the Entry Editor, set the Type of entry to Add-In, click Select Add-In and select the Event Log Monitor.
Click on the Configure Add-In button.
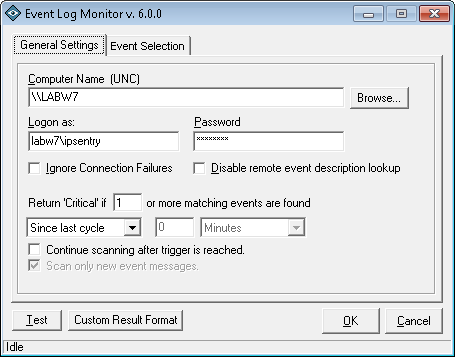
Event Log Monitor Configuration - General Settings
After selecting to Configure Add-in from the main ipSentry Entry Editor, you will be presented with the event log monitoring configuration options.
Computer Name
If this field is left blank, the event logs to be scanned will be those on the local machine. You may enter a remote computer name here in the format of \\computername in order to monitor the event logs of the specified computer. Click on the Browse button to open the network browser and select a computer from your network list.Logon As
If the remote system requires you to logon under an account other than the account under which ipSentry is running, you will need to enter the logon user name here. Because of the myriad security logon restrictions and requirements within various networks, you may need to specify domain, computer, or just logon name.
For example: MYDOMAIN\MyUserName or MYCOMPUTER\MyUserName or just MyUserName
Troubleshooting:
** Validate accessibility to the remote machine event logs first by loading the windows Event Viewer and viewing the event logs through the windows utility. If you can not connect to the remote machine and obtain event log information using Event Viewer, ipSentry won't be able to access the logs either. Contact your system administrator to identify the requirements for access the remote system and viewing event logs from the ipSentry machine.
** Insure you can access the registry on the remote system from the ipSentry machine. The event log source information is contained within the registry on the system from which you are obtaining event log information. If the user specified does not have access to the HKLM registry hive, you will not be able to obtain the event log source information.
** Make sure that the ADMIN$ share is available to the user under which ipSentry is running, or the user you have specified in the Logon As field. ipSentry makes a connection to this share on the remote system to validate administrative access.Password
Enter the password associated to the account specified in the Logon As field.Ignore Connection Failures
This option will ignore failures to connect to the remote system and will only return a CRITICAL status if the event log can be scanned AND the filter specification is matched. This option should only be used after you have validated that your configuration is correct AND when you don't want any alerts to be triggered when a failure to connect occurs. Our recommendation is to leave this option unchecked.Disable Remote Event Description Lookup
When performing a keyword search of the event message text, the monitor must obtain both keywords that are stored in the event log as well as external text used to format the message for the event viewer. If the message DLL is not contained on local machine (for example, when you are monitoring events from a software package not installed locally), ipSentry will attempt to obtain the message format from the remote system. This can cause very long scan times as well as possible security messages in your remote event logs. In many cases, the message ID and message keywords are sufficient to identify a specific event and we recommend that you enable this option when scanning remote event logs to enhance performance.Return Critical if...
This field represents the number of matching event log messages that must be found in the log for the duration specified below. For example, you may not care if 1 spurious event (matching your filter) occurs here and there. However, if 4 or 5 or more occur in rapid succession, that may point to a critical issue that needs addressed immediately. Set this value to the number of events that must occur within the time-span specified below before you will be alerted.Since Last Cycle / Within Last (selection)
This field allows you to specified the time frame of the log file to be scanned for event messages matching your filter. By default, the event log monitor will scan all events logged since the last time it checked the event log.Since Last Cycle
Select this option to have ipSentry scan only new events within the event log. This option is the least resource intensive and fastest scanning option provided since it will only request event information that is new.Within Last
Select this option to specify a time-span of event entries that ipSentry should scan. For example, if you are looking for 3 security failure events within the last 24 hours, then you would set this option to Within Last, set the value to 24, and set the time frame to Hours. This will result in ipSentry scanning all events that have a date/time value within the last 24 hours in order to accumulate the total number of matching events.
Continue scanning after trigger is reached.
Select this option to keep ipSentry from stopping the scan once the filter criteria has been matched.
By default, ipSentry will stop scanning the log when the filter criteria has matched or it has scanned all records within the specified time frame - whichever comes first. With this option set, it will always evaluate every entry within the specified time frame whether or not the criteria was matched before the scanning was complete. This is much more resource intensive since it is requesting many entries that may not apply and will not affect the outcome of OK or CRITICAL return state.Scan only new event messages
If you select this option, the stop-point (baseline) within the log will automatically be set to the last point scanned. Basically, this option states that the time span set is the 'maximum' time frame to scan. For example, if you have set the time span for "Within Last 24 hours", and it is scanning every 20 minutes, it will only scan event messages since last cycle. If you shut down ipSentry for 4 days and this entry runs, it will scan "up to" 24 hours worth of new data and then get back on track.Test
When you select to Test, you may have the option to select a lower bounds date to identify an event that matches your filter. This test is only used to identify an event within a period of time in order to check even filter configuration against a known event in the log file.
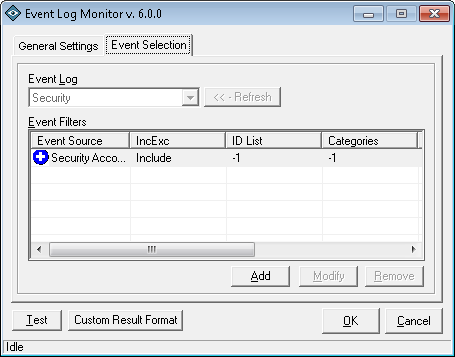
Event Log Monitor Configuration - Event Selection
The event selection tab displays the event log(s) and filters that are currently set in the configuration.Event Log Monitor Configuration - Filter ConfigurationEvent Log
This area allows you to select the event log that should be scanned for the entries outlined in the Event Filters Listing. Once you have event filters applied, this field is locked. In order to change the log file, you will need to remove the event filters since the sources available can only apply to one event log.Event Filters
List of currently configured event filters.Event Source
This column shows the event source that is set for this filter.IncExc
Include signifies that events matching this filter are 'included' in the event found count.
Exclude signifies that event matching this filter are ignored.ID List
List of Event ID #'s associated with this filter. -1=All ID'sCategories
List of Event Category #'s associated with this filter.-1=All Categories
Type Mask
This is a bit-mapped value for reverence only.User Names
This is a list of user-names to be matched for this filter.Contains
This is the text data that would appear in the event message.
** Note: Due to the location of the message information in some applications, the message information may not be available. Some applications store common message strings in message files located on the remote computer. Due to security and path limitations, these files may not be accessible and therefore, some data may not be available to the event log add-in. Fortunately, most operating system events will contain the necessary information.Add (button)
Click this button to add a new event filter.Modify (button)
Click this button to edit the currently selected event filter.Remove (button)
Click this button to remove the currently selected event filter.
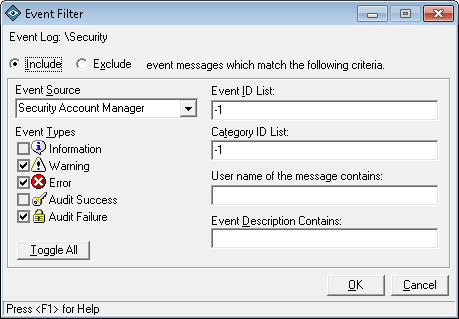
The event filter configuration is used to specify the Source, Type, ID's, Categories, User Name, Description and Inclusion/Exclusion of an event log entry.
Include
Selecting this option signifies that events matching the configuration should be considered as matching events and should trigger an alert so long as the event does not match any of the Exclude filters.Exclude
Once an event is found that matches an Include filter, the event will be evaluated against any Exclude filters. If the event matches an exclude filter, it will be ignored.Event Source
Select the source of the event. You can find this value in the Windows Event Viewer in the Source column associated with the event you wish to evaluate.Event Types
The event type is a bitmapped value that denotes the classification of the event such as Information, Warning, Error, Audit Success and Audit Failure.Event ID List
This field may contain an Event ID number or a list of Event ID numbers (separated by comma) that are acceptable for this entry. If you wish to consider ALL event ID numbers, enter a -1 in this field.Example:
An entry of 538,528 in this field would signify that only events with event ID 538 or 528 are acceptable.Category ID List
Similar to the Event ID List, this field may contain a Category ID number or a list of Category ID numbers (separated by comma) that are acceptable for this entry. The category ID number is of course unique to the application generating the event. If you wish to consider ALL category ID numbers, enter a -1 in this field.User Names
Each event contains a the account name of the user that logged the event. You can filter events based on none, one, or more usernames by entering the user name(s) in this field (separated with comma). Leave this field blank to consider events logged by any user.
Example:
An entry of SYSTEM, Administrator, ANONYMOUS would cause the add-in to evaluate only events that were logged by these users. e.g. DOMAIN\Username
Note that accounts such as SYSTEM may be returned as "\SYSTEM" - no domain prefix.Event Description
The information in this field will be compared against the message text in the event log.
** Note: Due to the location of the message information in some applications, the message information may not be available. Some applications store common message strings in message files located on the remote computer. Due to security and path limitations, these files may not be accessible and therefore, some data may not be available to the event log add-in. Fortunately, most operating system events will contain the necessary information.